The enterprise prospect’s security team sent you a questionnaire. Somewhere in the middle of 47 questions about your security program, there’s a line: “Do you have a SOC 2 Type II report?” You know what HIPAA is. You’ve been building toward HIPAA compliance since day one. SOC 2 is something else, and you’re not sure whether it’s the same thing with a different name, something you should have had already, or something that can wait until the deal is bigger.
For SOC 2 for healthcare startups, the direct answer is this: SOC 2 is not HIPAA. It is not a substitute for HIPAA, and HIPAA is not a substitute for it. They address different questions, required by different audiences, for different purposes. If you’re selling to enterprise buyers — health systems, payers, large employers — you will eventually need both. The question is when, in what order, and at what cost.
This piece delivers four things: a clear explanation of what SOC 2 is and what it isn’t, how it overlaps with and differs from HIPAA, a realistic cost breakdown for healthcare startups at different stages, and the specific signals that tell you when to start.
When does a healthcare startup need SOC 2?
When enterprise buyers — health systems, payers, or large self-insured employers — appear in your pipeline and their procurement teams ask for a SOC 2 report. HIPAA remains the legal baseline for any product handling PHI, but SOC 2 is the market signal that unlocks enterprise deals, and Type II takes 10–14 months from a standing start with automation tooling.
Key Takeaways
- SOC 2 is cheap relative to the deals it unlocks. Type II runs $39K–$70K all-in with automation tooling; a single health system or payer contract is worth multiples of that. The expensive mistake isn’t audit spend — it’s missing the deal because the report wasn’t ready.
- The sequence is HIPAA first, Type I when asked, Type II proactively. HIPAA is the legal baseline for any product handling PHI. Type I opens the first enterprise conversation. Type II is the report procurement teams actually want — start it 12 months before your enterprise pipeline gets serious.
- Pipeline signals trigger SOC 2 healthcare compliance, not stage or revenue. A security questionnaire, deals lost to competitors with SOC 2 reports, or an LOI conditional on the report is the trigger. Start earlier and you waste runway; wait until a deal is blocked and you’re too late.
Table of Contents
- What SOC 2 Actually Is and What It Isn’t
- SOC 2 vs. HIPAA — The Comparison Every Healthcare Founder Needs
- How Much Does SOC 2 Cost for a Healthcare Startup?
- When Do You Actually Need SOC 2?
- SOC 2 vs. HITRUST vs. ISO 27001 — Which Framework for Healthcare?
- The SOC 2 Readiness Checklist for Healthcare Startups
- The SOC 2 Timeline — What 12 Months Actually Looks Like
- Why Choose Topflight as Your HIPAA-Compliant Health App Development Partner
What SOC 2 Actually Is and What It Isn’t
SOC 2 (System and Organization Controls 2) is an auditing standard developed by the AICPA that evaluates whether a company’s information security controls meet specified criteria across security, availability, confidentiality, processing integrity, and privacy. A SOC 2 report is produced by an independent CPA auditor after reviewing your systems and control environment against those criteria.
What makes SOC 2 different from a compliance checklist: it is an auditor’s professional assessment of whether controls are designed and operating effectively, not a fixed pass/fail test. The outcome depends on which criteria you include in scope and what the auditor finds.
SOC 2 Type I vs. Type II — The Distinction That Matters
This is the first question every founder asks when they receive a SOC 2 request.
- SOC 2 Type I: A point-in-time assessment. The auditor evaluates whether controls are designed appropriately as of a specific date and answers the question, “Do you have the right controls in place today?” Takes 6–10 weeks to complete with prior preparation. Often sufficient to open a first enterprise conversation.
- SOC 2 Type II: An operating effectiveness assessment over an observation period of 3–12 months (first-time audits typically run 6 months). The auditor evaluates whether controls actually worked throughout the observation period and answers, “Have your controls been operating effectively for the past [X] months?” Takes 6–18 months from initial readiness to report completion. For healthcare startups, SOC 2 Type II healthcare procurement requirements mean this is the report enterprise health systems and payers actually want to see on their vendor intake forms.
The investment difference between the two is significant — see the cost breakdown below for specifics by approach.
Common Mistake: Most enterprise procurement teams specifically request Type II, not Type I. Early-stage startups can use Type I to open initial conversations but should plan for Type II within 12–18 months. Misrepresenting Type I as equivalent to Type II is a procurement relationship risk.
The Five Trust Services Criteria — Which Ones Healthcare Startups Need
You choose which Trust Services Criteria (TSC) your audit covers. More criteria means more cost and more audit scope. Here is the healthcare-relevant breakdown:
- Security (CC — Common Criteria): The security trust service criteria cover logical access controls, change management, risk assessment, incident response, and vendor management. Baseline — required in every SOC 2.
- Availability criteria: System uptime commitments. Include for clinical workflows where downtime has patient-care implications.
- Confidentiality criteria: Protection of information designated confidential. Most healthcare SaaS agreements include confidentiality commitments, which is what pulls this criterion into scope.
- Privacy criteria: Aligned with GDPR and CCPA. Include if your product collects consumer health data and you want a privacy signal beyond HIPAA.
- Processing integrity criteria: Relevant for analytics, billing, and claims-adjacent tools. Usually not required for most healthcare apps.
Healthcare startup default scope recommendation: Security + Availability + Confidentiality. This is the three-criteria scope that satisfies the vast majority of health system and payer procurement questionnaires without over-engineering the audit scope for early-stage companies.
SOC 2 vs. HIPAA — The Comparison Every Healthcare Founder Needs
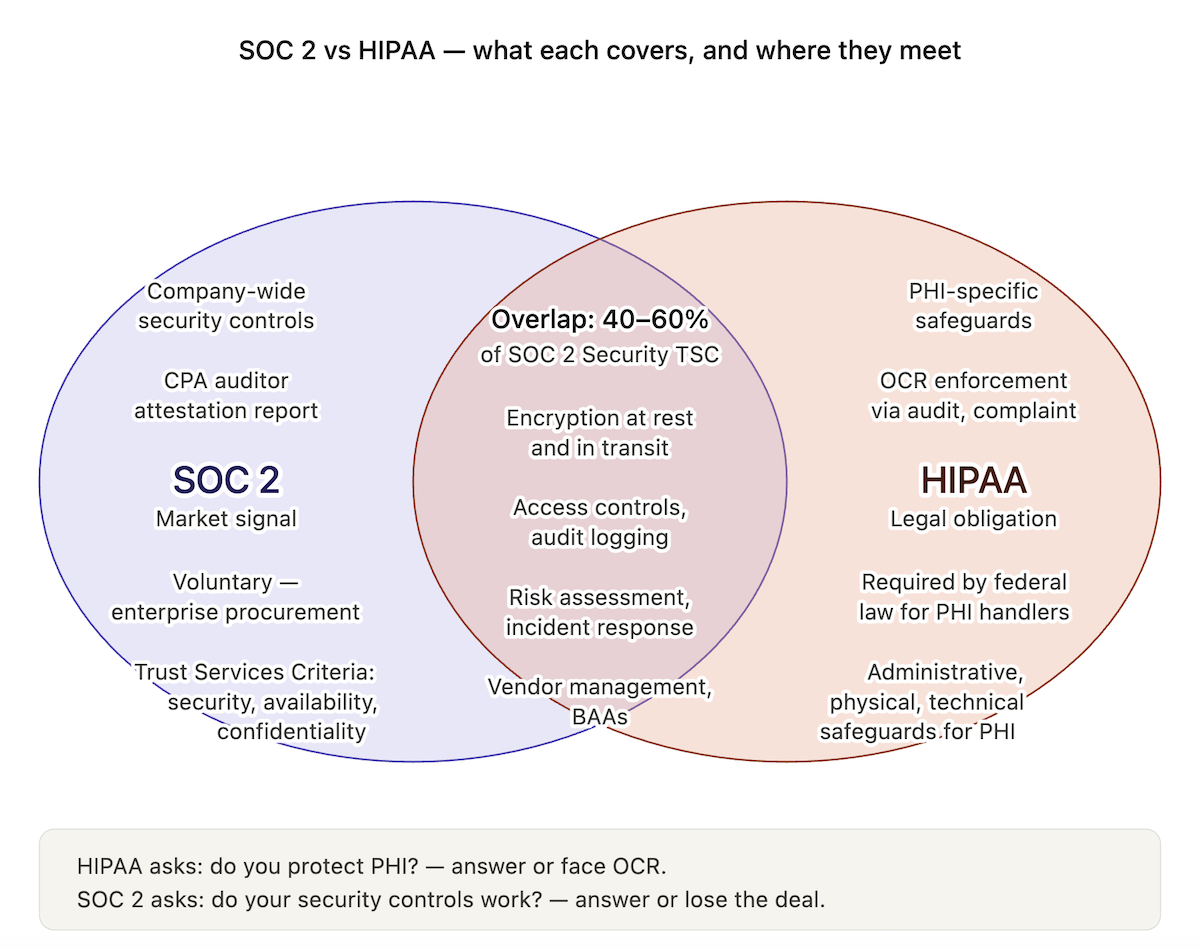
SOC 2 and HIPAA are not alternatives. They coexist, answering different questions for different audiences, and healthcare startups selling to enterprise buyers eventually need both.
Before deciding which to prioritize, look at the SOC 2 vs HIPAA healthcare distinction side by side: the two frameworks overlap in spirit but diverge sharply on who requires them, how they’re obtained, and what they cover.
| Dimension | SOC 2 | HIPAA |
| What it covers | Your company’s information security controls across all data, not just health data | Protection of protected health information (PHI) specifically |
| Who requires it | Enterprise customers (health systems, payers, employers) in procurement / vendor assessment | Federal law — required of covered entities and business associates regardless of customer demand |
| Who issues it | Independent CPA auditor produces a formal report | Self-attested compliance; OCR enforces via audit and complaint investigation |
| Legal obligation | No — it is a voluntary, market-driven attestation | Yes — HIPAA compliance is a legal requirement if you handle PHI |
| Focus | Security posture of your entire organization and technology stack | Privacy and security of health data specifically |
| Frequency | Type I: point-in-time; Type II: observation period of 3–12 months (first audit often 3–6 months, then annual 12-month cycles with yearly renewal) | Ongoing obligation; risk assessment should be updated annually or when systems change |
| Cost | $15K–$80K+ for audit depending on scope and type | No direct audit cost; remediation costs vary widely |
| Time to obtain | Type I: 6–10 weeks; Type II: 6–18 months from readiness start | No formal ‘certification’ to obtain; ongoing compliance program |
| PHI-specific controls | Privacy TSC covers personal data broadly; no PHI-specific controls | Detailed technical, administrative, and physical safeguard requirements for PHI specifically |
| Customer-facing value | Provides a standardized, auditor-verified security signal to enterprise buyers | Table stakes for any product touching PHI; buyers assume it, they don’t reward it |
| Do you need both? | Eventually yes, if selling to enterprises in healthcare. SOC 2 is the enterprise sales signal; HIPAA is the legal baseline. | Yes, if your product touches PHI. Non-negotiable regardless of SOC 2 status. |
Key Insight: HIPAA is a legal obligation — you either comply or you don’t, and the penalty for non-compliance is regulatory. SOC 2 is a market signal — you either have it or you don’t, and the consequence of not having it is lost deals.
A healthcare startup can be fully HIPAA compliant and have no SOC 2 report. Many are. They lose enterprise deals to competitors with SOC 2 because enterprise procurement teams treat HIPAA compliance as assumed (they’ll ask for your BAA) and SOC 2 as a differentiating security signal. A health system’s vendor assessment process doesn’t reward the HIPAA baseline; it filters on what sits above it, which is why HIPAA compliant software development should start from day one, not as an afterthought once a deal appears.
The inverse case: a startup can theoretically hold SOC 2 without being HIPAA compliant. For any product touching protected health information (PHI), that’s reckless. SOC 2’s security criteria cover information security broadly; HIPAA covers PHI specifically and is the legal obligation SOC 2 does not replace. An OCR audit can be triggered regardless of SOC 2 status — by a complaint, a breach, or random selection — and even tool choices like ChatGPT HIPAA compliance fall under HIPAA’s reach, which SOC 2 alone won’t address.
How Much Does SOC 2 Cost for a Healthcare Startup?
“How much does SOC 2 cost for a healthcare startup?” depends on which of three approaches you take. Costs vary by current security posture, company size, and whether you use compliance automation.
The table below breaks down all-in costs across DIY, automation-assisted, and full-service consultant-led paths.
| Cost Component | DIY (No Automation) | Automation-Assisted (Vanta/Drata) | Full-Service (Consultant-Led) |
| Compliance automation platform | $0 | $12,000–$20,000/year | $0 (consultant-managed) |
| Readiness gap remediation (engineering time) | $20,000–$60,000 (unguided = inefficient) | $10,000–$25,000 (automation identifies gaps) | $15,000–$30,000 (consultant scopes remediation) |
| Policies and procedures (writing) | $5,000–$15,000 (attorney or internal) | $2,000–$5,000 (templates + customization) | $5,000–$10,000 (consultant delivers) |
| CPA auditor fees (Type I) | $12,000–$20,000 | $8,000–$15,000 (automation reduces audit prep) | $15,000–$25,000 (auditor bundled with consultant) |
| CPA auditor fees (Type II, annual) | $20,000–$40,000 | $15,000–$25,000 | $25,000–$45,000 |
| Internal time cost (FTE hours) | High — 300–500 hours year 1 | Medium — 100–200 hours year 1 | Low — 50–100 hours year 1 |
| Consultant management / retainer | $0 | $0 | $10,000–$25,000 |
| TOTAL — Type I (first year) | $37,000–$95,000 | $32,000–$65,000 | $35,000–$65,000 |
| TOTAL — Type II (first year, from scratch) | $45,000–$115,000+ | $39,000–$70,000 | $55,000–$110,000 |
| TOTAL — Type II (renewal years) | $25,000–$50,000 | $27,000–$45,000 (platform + annual audit) | $30,000–$55,000 |
For healthcare startups from Seed through Series B, automation-assisted is the recommended default. The platform handles continuous monitoring of your control environment, auto-collects evidence, and significantly reduces both auditor prep time and internal engineering effort. The $12K–$20K/year platform cost is typically recovered in the first audit cycle through reduced auditor prep plus drastically lower internal lift; teams save 200–300 engineering hours versus a DIY approach. Healthcare startups most commonly evaluate Vanta, Drata, Secureframe, and Sprinto. Each covers the SOC 2 control set adequately; the differentiation is in integrations, pricing, and UX rather than core capability.
Common Mistake: Starting SOC 2 without a readiness assessment. Teams spend 3–6 months remediating controls that weren’t even in scope, then discover critical gaps right before the audit window closes. A readiness assessment ($5K–$15K from a consultant, or free from an automation platform) identifies the actual gap before a dollar is spent on remediation. Healthcare teams that built their MVP fast with AI coding assistants, the vibe coded health app real health data pattern, typically see the biggest remediation bills when they finally run the gap analysis.
How HIPAA Work Reduces SOC 2 Cost
A mature HIPAA compliant app development program generates artifacts (risk assessments, encryption controls, access logs) that map directly onto SOC 2 requirements. The overlap between HIPAA Security Rule safeguards and SOC 2’s Security Trust Services Criteria is substantial:
- Risk assessment → SOC 2 risk assessment controls
- Encryption at rest and in transit → SOC 2 logical access and data protection controls
- Audit logging → SOC 2 monitoring controls; control mapping between HIPAA and SOC 2 audit log requirements is direct
- Access controls and minimum necessary → SOC 2 logical access controls
- Incident response plan → SOC 2 incident management
- Vendor management and BAAs → SOC 2 vendor risk management
Key Insight: A healthcare startup with a mature HIPAA program can have 40–60% of SOC 2 Security TSC controls already in place. The incremental cost of SOC 2, on top of a solid HIPAA foundation, is significantly lower than starting from scratch. This is the HIPAA SOC 2 overlap that lets you stack them efficiently.
Topflight can assess how much of your existing HIPAA program overlaps with SOC 2 requirements before you invest in the audit process.
When Do You Actually Need SOC 2?
Not immediately, not never. Start SOC 2 when an enterprise signal appears in your pipeline — not upon incorporation, and not after a deal is already blocked. When do I need SOC 2 for health tech? For startups navigating health system enterprise sales, the answer depends on specific signals in your pipeline rather than a fixed stage or revenue threshold.
The Readiness Signals Matrix
| Signal | Type Needed | Urgency | What to Do |
| Enterprise prospect (health system or payer) has included SOC 2 in their security questionnaire | Type I minimum; Type II preferred | Immediate | Start readiness assessment this week. Type I can close the immediate gap while you run the Type II observation period. |
| Sales team is consistently losing deals to competitors who have SOC 2 reports | Type II | Soon | SOC 2 is now a competitive prerequisite in your target market. Begin observation period immediately — every month you wait delays your Type II report by one month. |
| Series B fundraise on the horizon (within 12 months) | Type II | Plan ahead | Investors at Series B increasingly treat SOC 2 as a portfolio hygiene requirement. Start now — Type II takes 12–18 months from scratch. |
| Health system or payer has signed LOI but procurement requires SOC 2 before contract execution | Type I as bridge; Type II commitment | Immediate | Negotiate Type I as sufficient for initial contract; commit to Type II delivery within 12 months. Most sophisticated procurement teams with payer compliance experience will accept this structure. |
| Serving SMB/mid-market healthcare customers only; no enterprise sales pipeline | Neither — yet | Optional | HIPAA compliance is still required. SOC 2 can wait until enterprise pipeline materializes. Revisit in 6 months. |
| Government or federal health program contract (CMS, VA, DoD health) | FedRAMP may apply instead | Plan ahead | Federal health contracts may require FedRAMP, not SOC 2 — and if your product is clinical AI, you may also be navigating health AI FDA clearance on a parallel track. Engage a compliance consultant before starting any audit process. |
| Platform processes data on behalf of another covered entity (you are a BA) | SOC 2 Type II strongly recommended | Plan ahead | Your covered entity customers may require SOC 2 as part of their vendor risk management. HITRUST is also common in this scenario — assess both. |
Start SOC 2 when it’s in your pipeline, not when it’s blocking a deal. The math: a first-time Type II observation period of roughly 6 months plus 3–6 months of audit-ready preparation means 12–18 months is the earliest possible delivery if you’re starting cold. By then, the deal that triggered the scramble has already moved on to the vendor who started earlier.
Common Mistake: Waiting until an enterprise prospect says “no SOC 2, no deal” before starting. By that point, the best you can offer is a Type I report in 8–10 weeks (which may or may not satisfy procurement) plus a Type II commitment 12–18 months out. Procurement teams with firm timeline requirements will move on.
The discipline is starting SOC 2 readiness roughly 12 months before enterprise procurement conversations get serious — which means starting when those conversations first become plausible, not when they are already on the table.
SOC 2 vs. HITRUST vs. ISO 27001 — Which Framework for Healthcare?
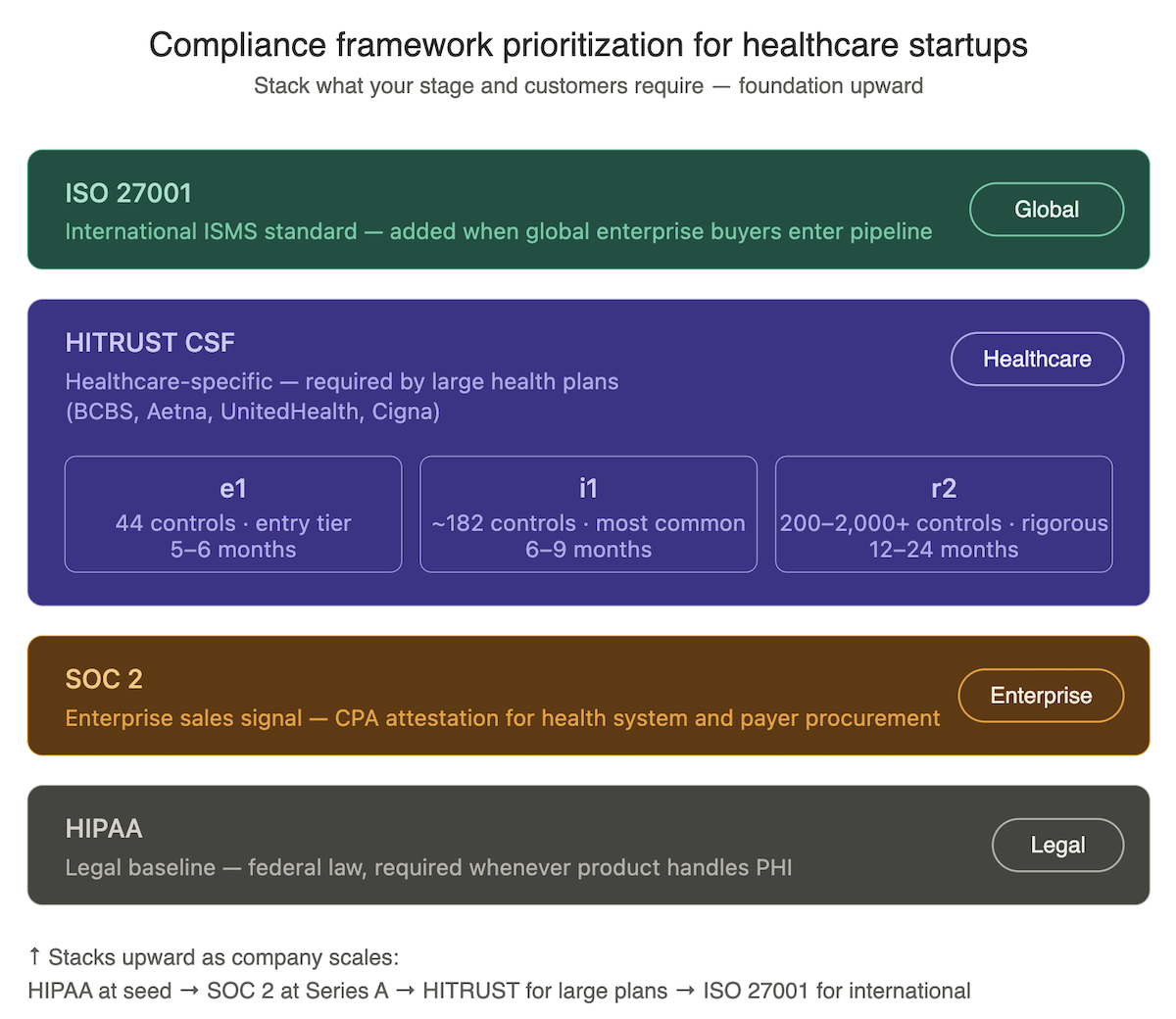
Healthcare enterprise procurement teams may request any combination of SOC 2, HITRUST, or ISO 27001. The SOC 2 vs HITRUST healthcare question usually comes down to which customers you’re selling to and where they sit on the vendor-maturity spectrum. Here is when each is relevant:
HITRUST CSF — The Healthcare-Specific Framework
HITRUST (Health Information Trust Alliance) Common Security Framework is a healthcare-specific certification that maps HIPAA, SOC 2, NIST, ISO, and other frameworks into one control set. It’s the most comprehensive and expensive of the three, required by a subset of enterprise buyers — particularly large national health plans and health systems with mature vendor risk programs.
- Cost: $20K–$200K+ for initial certification depending on tier. HITRUST offers three — e1 (44 controls, fastest and cheapest entry), i1 (~182 controls, most common for healthcare vendor contracts), and r2 (200+ controls, most rigorous). Annual renewal runs $10K–$80K depending on tier.
- Timeline: 5–24 months for first certification depending on tier.
- When required: Large health plan (BCBS, Aetna, UnitedHealth Group, Cigna) vendor requirements; some large health system RFPs; government-adjacent health programs.
- SOC 2 overlap: HITRUST maps to many SOC 2 controls, but a HITRUST certification alone is not a SOC 2 report — customers requesting SOC 2 want the actual attestation. A combined SOC 2 + HITRUST assessment, performed by a CPA firm that is also an authorized HITRUST assessor, produces both deliverables in one engagement.
ISO 27001 — The International Standard
ISO 27001 is the international information security management system standard. It’s more common in non-US markets and in large enterprise and government contexts. For US healthcare startups selling primarily to domestic health systems and payers, ISO 27001 is rarely a priority over SOC 2.
- Cost: $15K–$80K for initial certification (the low end reflects small startups using compliance automation; mid-market reaches $80K+). Annual surveillance audits in years 2 and 3 run 30–50% of initial cost, with a full recertification audit at year 3.
- When required: International healthcare customers; large enterprise with global procurement standards; occasionally required alongside SOC 2 for multinational health tech deals.
The Prioritization Framework for Healthcare Startups
Here is how digital health compliance priorities typically sequence as a healthcare startup scales:
- Seed / Pre-Seed: HIPAA compliance only. SOC 2 is premature.
- Series A / first enterprise conversations: SOC 2 Type I to open conversations; begin Type II observation period.
- Active enterprise pipeline with health system and payer targets: SOC 2 Type II as top priority. If your product includes AI features, AI in healthcare compliance considerations stack on top of your SOC 2 work.
- Targeting large national health plans or health systems with mature vendor programs: Assess HITRUST requirement; a combined SOC 2 + HITRUST assessment is often the efficient path.
- International sales or global enterprise customers: ISO 27001 added alongside SOC 2.
The SOC 2 Readiness Checklist for Healthcare Startups
Before engaging an auditor, confirm the following are in place. Missing items will be found during the audit and will delay your report. This SOC 2 readiness assessment is the version Topflight uses with SOC 2 digital health startup clients — healthcare-specific, not generic SaaS.
Security Policies and Procedures
Your auditor will want the following security policies documented, approved by leadership, and communicated to employees:
- Information security policy written and approved by leadership
- Acceptable use policy documented
- Access control policy: how access is granted, reviewed, and revoked
- Incident response plan: documented, tested, includes HIPAA breach notification procedure
- Vendor management policy: how third-party vendors are assessed and monitored — this is your vendor risk management program, and it’s one of the highest-scrutiny controls for health tech auditors
- Business continuity / disaster recovery plan
- Change management policy for software deployments
Technical Controls
Controls must be implemented, documented, and actively operating — not just written into policy:
- Multi-factor authentication enforced for all systems containing customer data
- Encryption at rest and in transit for all production data
- Audit logging for all access to PHI and sensitive data
- Vulnerability management program: regular scanning, patching SLA documented — particularly critical for teams shipping HIPAA compliance for AI-generated code, where AI-assisted commits can introduce controls gaps that standard scanners miss
- Penetration testing completed within the last 12 months
- Background checks completed for all employees with PHI access
- Employee security training completed and documented — awareness training for all staff plus role-specific training for engineering and anyone with PHI access
Access Management
Access management is the most sample-heavy control area in the audit. Expect the auditor to pull specific user accounts and trace them to documented approvals, role assignments, and quarterly reviews:
- Quarterly access reviews conducted — all active accounts verified against current employees/contractors
- Termination procedure documented: access revoked within 24 hours of employee departure
- Principle of least privilege enforced: employees have only the access required for their role
- Shared/generic accounts eliminated from all production systems
Healthcare-Specific Controls
These four items are where healthcare SOC 2 readiness diverges from generic SaaS readiness:
- HIPAA business associate agreements (BAAs) executed with all PHI-handling vendors (supports both HIPAA compliance and SOC 2 vendor management)
- PHI data flow documented: where PHI is created, stored, transmitted, and disposed — PHI-dense applications like behavioral health products have intricate flows (see therapy chatbot compliance for a worked example of this documentation discipline)
- Breach notification procedure aligned with HIPAA 60-day OCR notification requirement
- HIPAA risk assessment completed and documented — maps directly to SOC 2 risk assessment control
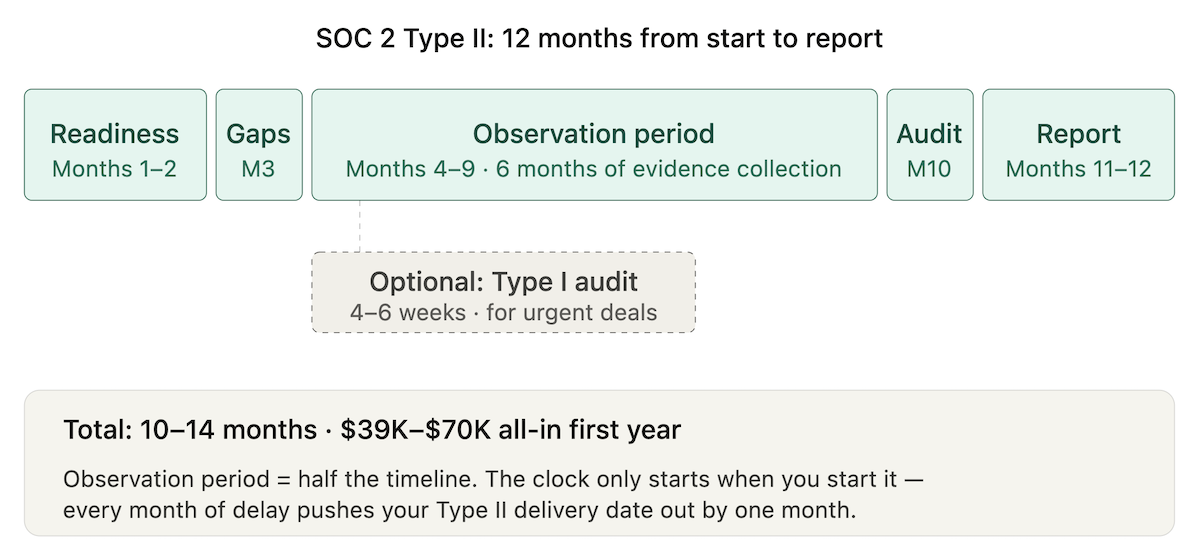
The SOC 2 Timeline — What 12 Months Actually Looks Like
Here is a realistic SOC 2 audit timeline healthcare startups can plan against when pursuing Type II from a standing start with automation tooling — month by month. This assumes a founding team engaged in the process from week one, an automation platform connected early, and no major architectural rebuilds required during remediation.
- Months 1–2: Readiness assessment. Select compliance automation platform (Vanta, Drata, or equivalent). Connect your AWS/GCP/Azure, GitHub, Okta/Google Workspace, and other integrations. Platform surfaces current control gaps. Begin policy library. Identify auditor.
- Month 3: Gap remediation sprint. Engineering implements missing technical controls: MFA enforcement, access review workflows, vulnerability scanning, logging gaps. Teams that built their MVP with AI coding tools often find the remediation sprint is where they discover whether their Cursor HIPAA compliant foundations were built correctly. Policies finalized and approved. Employee training deployed.
- Month 4: Type I audit option. If an enterprise deal requires immediate evidence of SOC 2 progress, a Type I audit can be conducted now — typically 4–6 weeks for report delivery. Type I report demonstrates controls are designed; does not replace Type II.
- Months 4–9: Type II observation period. All controls operating. Evidence collection runs automatically via the platform. Quarterly access reviews conducted. Penetration test scheduled and completed. No new critical findings from vulnerability scans.
- Month 10: Auditor fieldwork. Auditor reviews evidence collected during observation period, conducts interviews, tests control operation. 4–8 week process.
- Month 12: Type II report delivered. Audit opinion issued. Report shared with enterprise prospects under NDA.
Total calendar time from start: 10–14 months to Type II report. Total all-in cost with automation tooling: $39K–$70K first year. The Type II audit period sets the floor on delivery: every month the observation period hasn’t started is a month added to the total.
Key Insight: The single biggest time-saver in the SOC 2 process is starting the observation period early — even before all controls are fully optimized. The clock on the Type II observation period doesn’t start until you start it. Every month you delay starting the observation period is a month added to your Type II delivery date.
Why Choose Topflight as Your HIPAA-Compliant Health App Development Partner
Topflight builds HIPAA-compliant health applications with the technical control architecture that makes SOC 2 achievable without a ground-up security engineering effort. When compliance is designed into the cloud security posture from day one — audit logging, encryption, access controls, BAA-eligible infrastructure — the readiness checklist is mostly already complete by the time your first enterprise conversation begins.
What we bring to healthcare startups preparing for enterprise procurement:
- HIPAA-compliant architecture: audit logging, field-level encryption, RBAC, and BAA-eligible infrastructure from the first commit
- SOC 2-relevant technical controls included by default: MFA enforcement, access review support, and logging that satisfies both HIPAA audit requirements and SOC 2 evidence collection
- Health data security gap analysis: assessment of your existing application against both HIPAA and SOC 2 Security TSC requirements
- Pre-enterprise readiness support: making your codebase, infrastructure, and documentation investor- and enterprise-audit-ready
If your roadmap includes SOC 2 health app enterprise sales — health systems, payers, self-insured employers — the cheapest path is the one where the architecture was already built for it. Talk to us before you start the audit, not after.
Frequently Asked Questions
Do I need SOC 2 if I already have HIPAA compliance?
HIPAA and SOC 2 answer different questions. HIPAA is a legal obligation for any product handling PHI; SOC 2 is a market signal enterprise procurement teams require when vetting vendors. If you sell to health systems, payers, or large self-insured employers, you’ll eventually need both. Being fully HIPAA compliant without SOC 2 is a common reason healthcare startups lose enterprise deals.
What is the difference between SOC 2 Type I and Type II?
Type I is a point-in-time assessment of whether your controls are designed appropriately as of a specific date, completed in 6–10 weeks. Type II is an operating effectiveness assessment over an observation period of 3–12 months (first-time audits typically run 6 months) that evaluates whether controls actually worked. Enterprise health system and payer procurement teams specifically want Type II.
Does this is not medical advice protect my app from FDA regulation?
It depends on where you start. From a standing start with no compliance program, plan for 12–18 months to a Type II report. With automation tooling (Vanta, Drata, or similar) and active founder engagement, 10–14 months is realistic. A Type I report on its own can be ready in 6–10 weeks if prior security hygiene is solid.
How long does SOC 2 take for a healthcare startup?
It depends on where you start. From a standing start with no compliance program, plan for 12–18 months to a Type II report. With automation tooling (Vanta, Drata, or similar) and active founder engagement, 10–14 months is realistic. A Type I report on its own can be ready in 6–10 weeks if prior security hygiene is solid.
How much does SOC 2 cost for a small health tech company?
For a Seed-to-Series B startup using compliance automation, a first-year SOC 2 Type II runs $39K–$70K all-in, covering platform, auditor fees, remediation, and policies. Renewal years drop to $27K–$45K. DIY without automation typically costs more ($45K–$115K+ first year) because internal engineering hours balloon.